
An intelligent, agentic lineup to shape behavior and reduce risk.

Briefings, nudges, and chats that shape behavior in the moment, and over time.
Auto-creation of risk cohorts by role, access, behavior, and threats through natural language input.
Precise behavior targeting, from sensitive data in AI, password sharing over Slack, MFA adoption, and more.
Content editor to streamline briefing video creation and AI generation from templates.
Mass-customized content based on brand, and by referencing role, access, tools, and policies.
Interventions sent immediately upon detection of risky behavior, right where people work.
Clear reporting on engagement, behavior improvement, and risk reduction over time.
Arm your people for the real-world threats coming their way
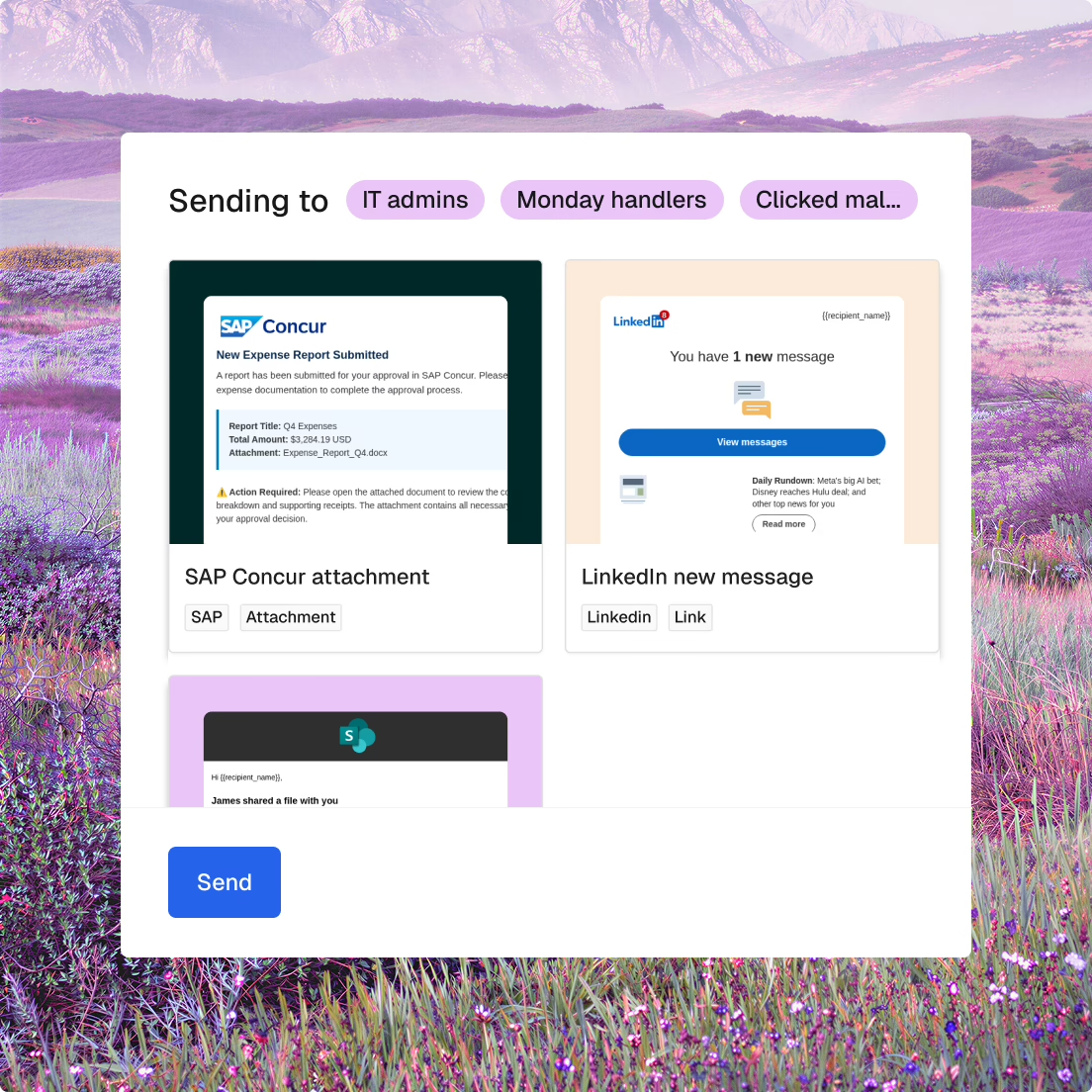
Tactics they’ll see in the real world: phishing, vishing, deepfakes, MFA bombing, LLM injection, and more.
Simulations tailored to employee role, application access, risk signals, and emerging threats.
Follow-up training mass-customized to each person’s errors, proven to reduce future offenses.
Deep reporting on phishing behavior—clicks, replies, credential entry, reporting, and response speed.
Accurate phishing results, minus the false positive clicks from bots and scanners.
Replace static training with targeted content tied to real threats, policies, and risky behaviors.
AI-customizable templates covering real-world topics—from phishing and MFA fatigue to data handling and compliance.
Training assigned based on risk—role, access, behavior patterns, and threat exposure.
Create and deploy training instantly for emerging threats—not months later like legacy programs.
Content automatically aligned to your company’s policies, approved tools, and security practices.
Automation that handles reminders, escalations, and reporting without manual administrative overhead.

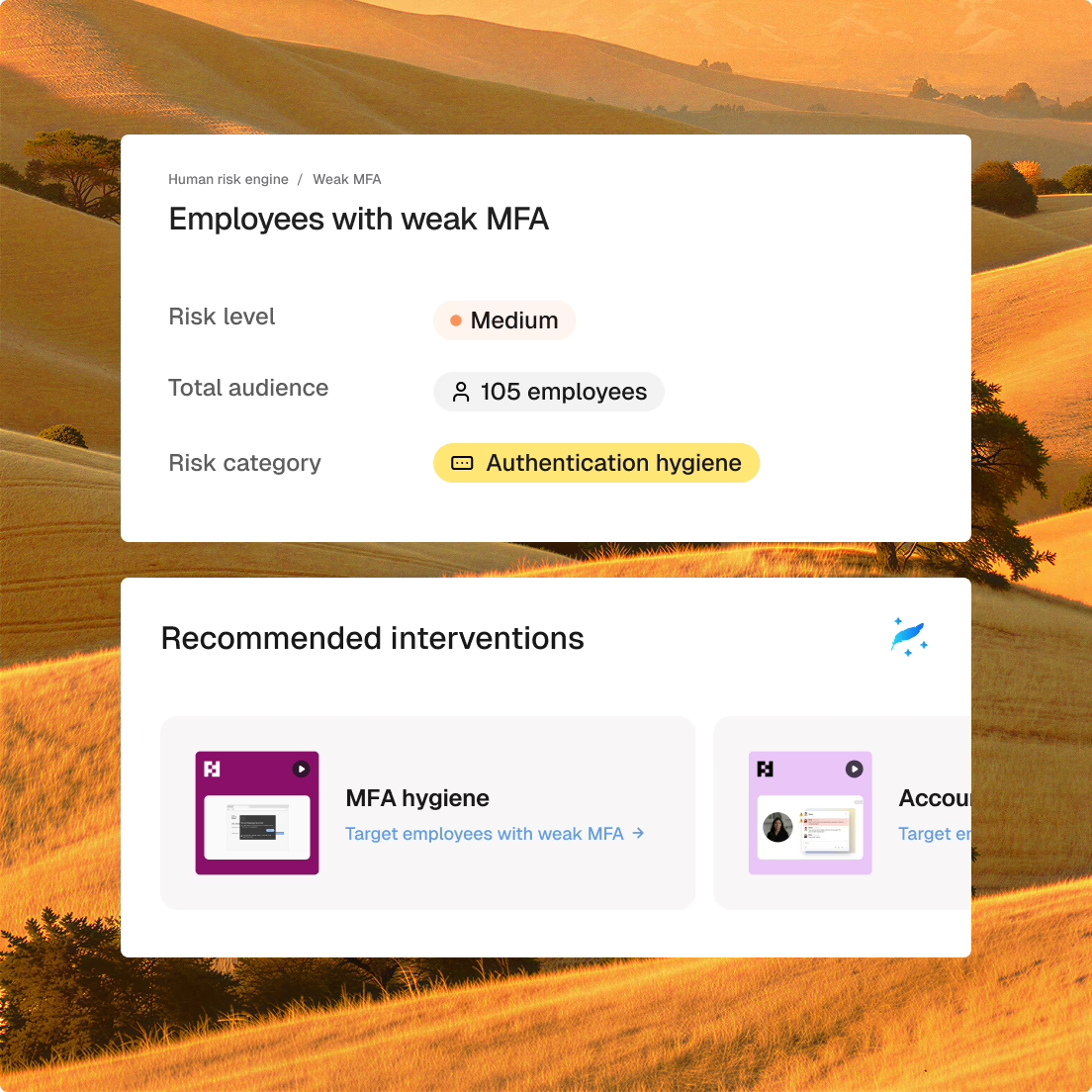
Understand human risk, what behaviors drive it, and what to do next.
Continuously updated human risk profiles based on employee behaviors and threat exposure.
Drill-downs into details that drive risk, including access, behaviors, and threat signals.
Auto-segmentation of risk by role, access, behavior, and threats through natural language input.
Structured guidance and recommended campaigns proactively teed up for specific risks.
Measurable engagement, behavior improvement, and risk reduction over time.


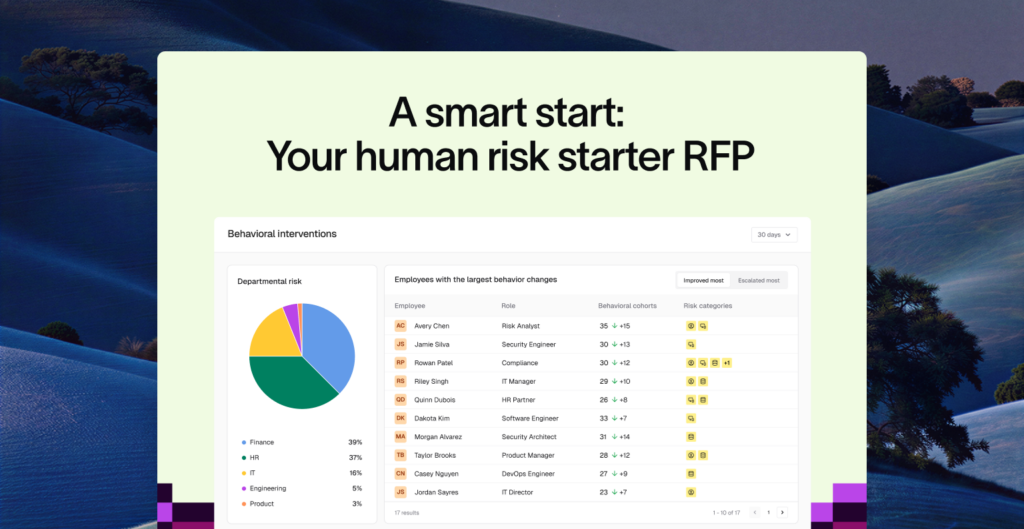
Kickstart your human risk management evaluation process with a pre-filled, editable RFP template.