Prove that you lowered human risk—not just sent a sim.
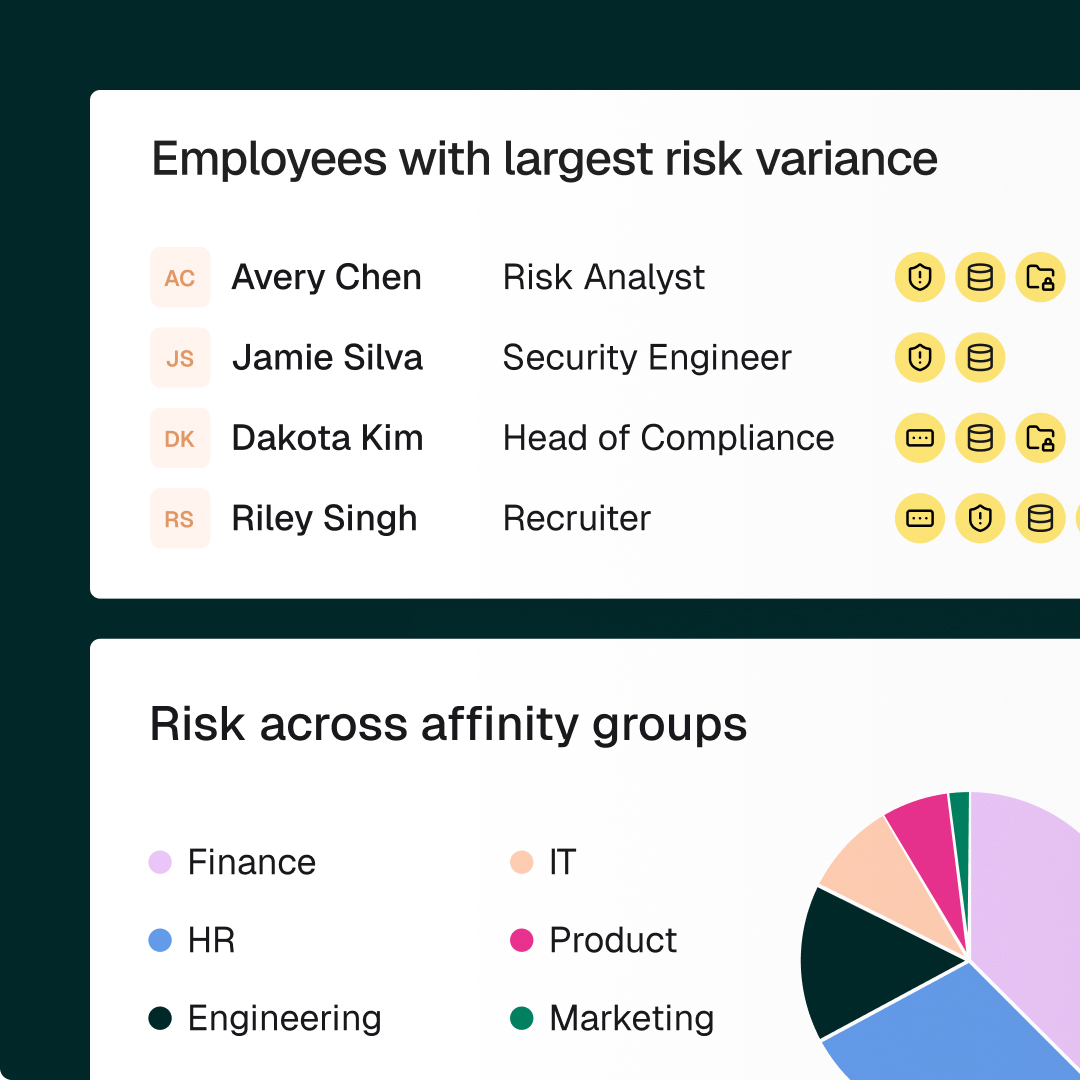
Legacy vendors guess who’s at risk. Fable finds out—then does something about it.


Security training campaigns and interventions designed to drive behavior change
Tracked behavior change to measure impact and adjust future training
Recommended campaigns and at-risk employee groups based on threats and known behaviors
Automatically reprioritized human risk categories based on employee behavior and threat changes
Automatically generated employee training groups, based on observed security habits and relevant traits
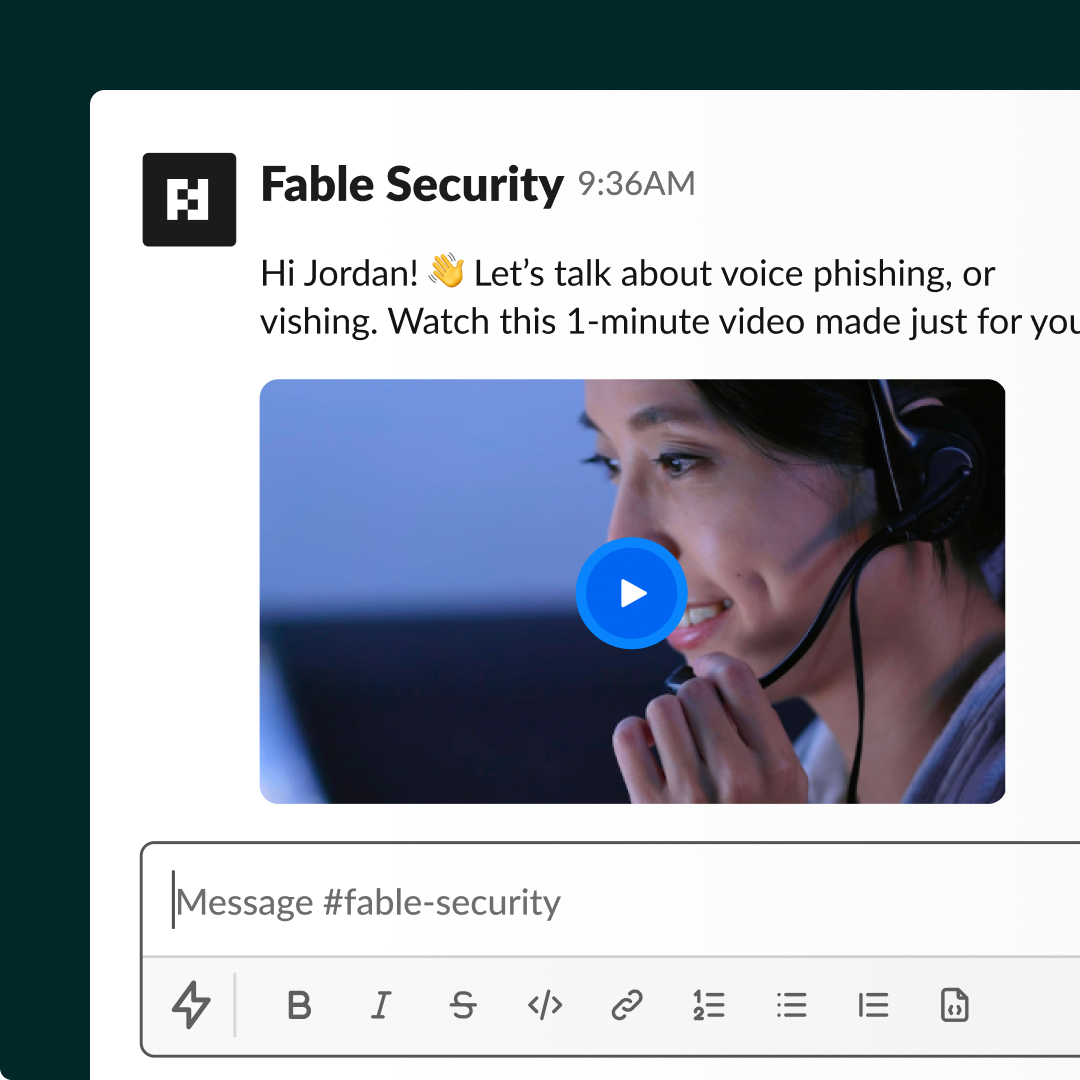
Training, reminders, and warnings delivered at risky moments
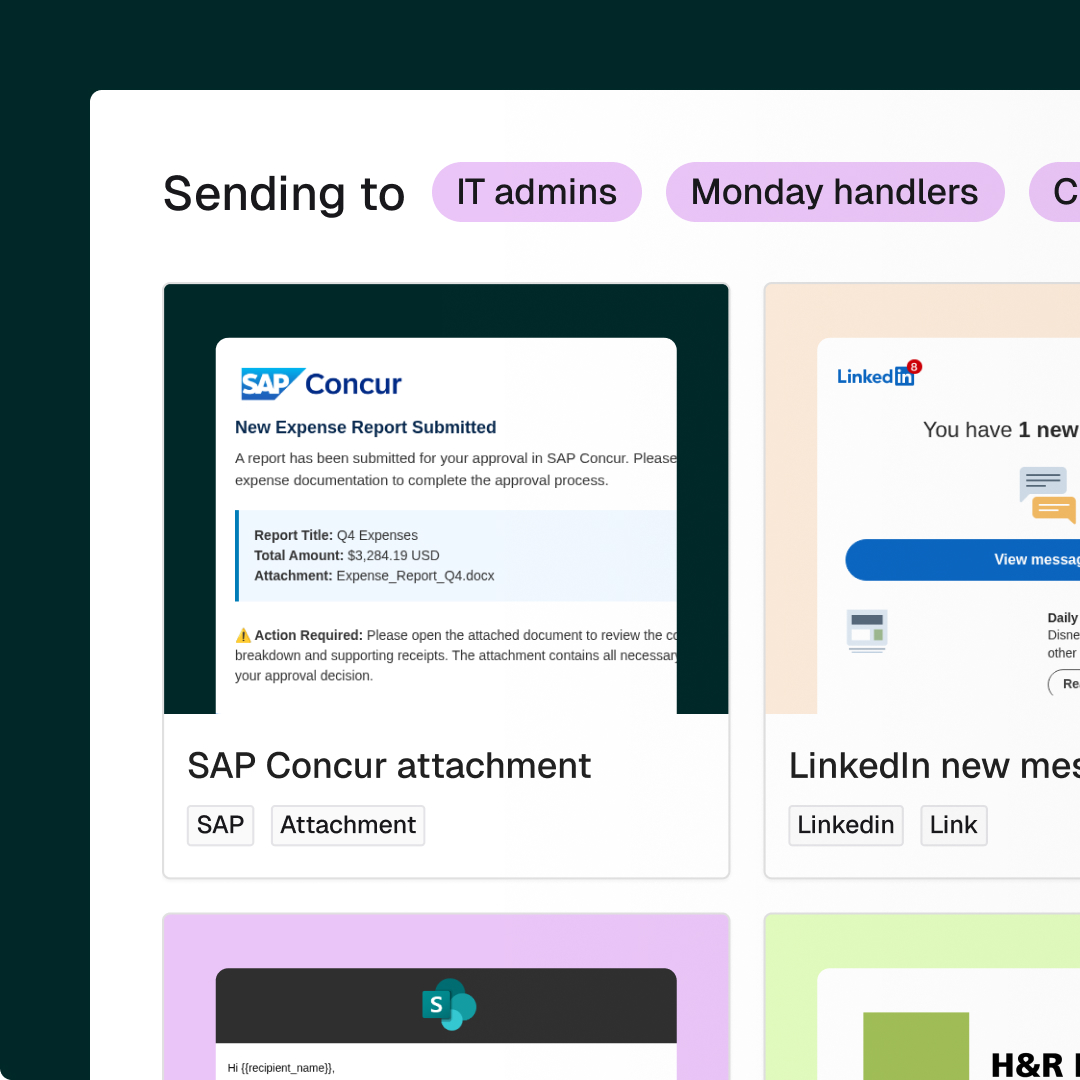
Templates for auto-generated, customized threat response briefings and simulations
SMS text and voice phishing emulations
On roadmap
1-2 minute video trainings and ~30 word reminders that don’t waste employees’ time
Tailored training for each person, policy, and process
Prebuilt templates for rapid, simple AI creation
Collected audience ratings and comments
Few-click security training, analysis, and reporting
Platform data security and privacy; secure infrastructure
Backend data lakehouse for scale and advanced behavior analysis

More than 100,000 pieces of direct feedback to-date with a 4.8 out of 5.0 average rating.