Ok. Deep breath as we head into the holidays.
There’s no great way to say this, but there was a recent extortion attempt of Mixpanel involving some Pornhub data attackers got in a breach. Beyond all the embarrassing fallout, it’s a reminder that companies don’t need to be directly hacked for sensitive data to end up in the wrong hands.
Here’s what went down: A hacking group known as Scattered Lapsus$ Hunters exploited a breach at Mixpanel, a widely used analytics provider, to access user data from multiple organizations, including Pornhub, OpenAI, and others. It’s a growing pattern in modern attacks: adversaries go after shared tools and services, then use the data they find to pressure or impersonate downstream targets.
For people, the risk isn’t abstract. Exposed information can include email addresses, locations, and detailed activity logs (in this case, the particular video someone watched—ai ai ai!). That data can be used to craft convincing phishing messages, impersonate trusted services, or attempt extortion by referencing private behavior. For organizations, the impact extends beyond the initial breach. Once attackers have this context, they often target employees directly, hoping urgency or embarrassment will prompt a quick response.
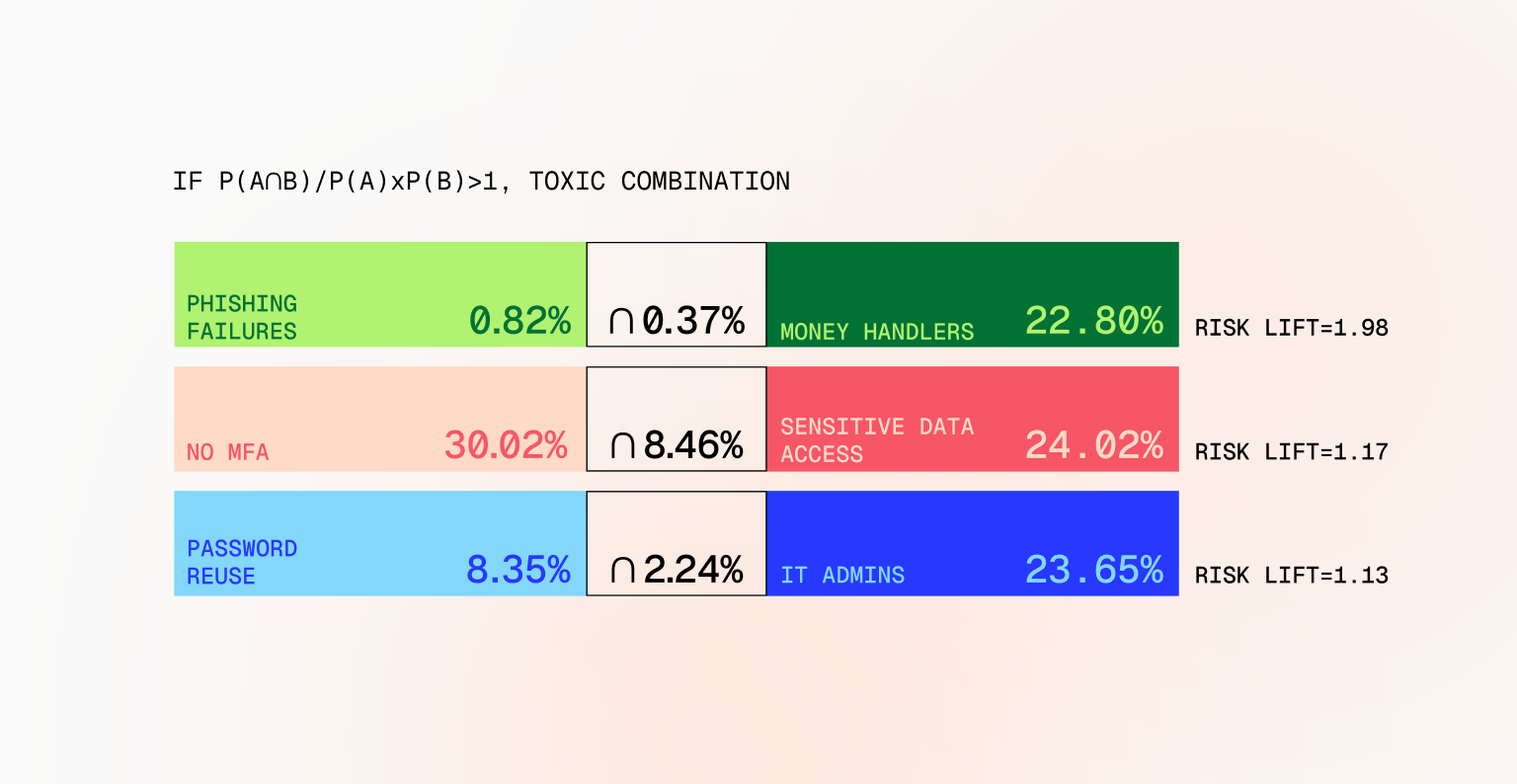
What should security teams do? First off, small actions make a big difference. Through your human risk program, warn people to keep an eye out for unexpected emails, especially those that reference account activity, subscriptions, or alleged security issues. They should pause before responding to unusual requests and verify them through official channels. They should never reuse passwords across sites, update impacted passwords, and enable strong multi-factor authentication. Also, they should try to decouple private behavior from identifying information as much as possible. At work, they should enable multi-factor authentication wherever possible. And if they become the victim of an extortion attempt by a bad actor claiming to have access to sensitive data, they should escalate the issue to the security team.
Beyond messaging to employees, security teams should stay alert for signs that internal users may be under pressure. Extortion attempts don’t always show up as external attacks—they can manifest as unusual behavior from otherwise trusted employees. Sudden requests for access, attempts to bypass controls, rushed approvals, or deviations from normal workflows can all be indicators that someone is being coerced. This isn’t about suspicion or blame, but recognizing that attackers increasingly target people directly, and ensuring there are clear, safe paths for employees to ask for help before a bad situation escalates.
To make this easier, Fable has created a short, 2-minute video that security teams can share internally to raise awareness about this type of third-party breach and the follow-on risks that come with it. It’s designed to be clear, practical, and non-alarmist, helping employees recognize what’s happening and what to do next. You can download and share the video for free below—and take a simple step toward reducing human risk before attackers have a chance to exploit it.