TL;DR—
Part four of six-part blog series on must-ask questions when creating net-new awareness training.
- Teams creating impactful security training should ask themselves, “What can employees actually do after they watch this security briefing?”
- Effective security training requires “cognitive closure”: connecting the dots between the new threat information and a desired behavior change that defends against it.
- Desired actions can include:
- Adopting better security habits related to the specific threat;
- Avoiding social engineering tricks and lures; and
- Proactively reaching out for help from the correct teams.
- See “Five must-ask questions for security training that changes employee behavior” for more questions Fable Security asks our clients before creating short-yet-impactful briefings!
Give panicked employees cognitive closure with calls to action in security briefings.
I ended last week’s post on target audiences for new security trainings and awareness briefings with the idea that who you sent a training to, depends on the desired outcomes of that training.
In other words:
What can the recipient of your new training personally do (or not do!) that will make your organization more secure?
When you teach someone about anything, there’s a natural impulse in the student to want to do something with that information. You have to give them an outlet to use what they’ve learned.
Otherwise, they’ll dismiss the knowledge as irrelevant—completely wasting the lesson (or the new custom briefing you spent so much time on).
In behavioral psychology terms, this phenomenon is related to cognitive closure: Individuals’ drive to determine a definite answer to a question, rather than exist in a state of uncertainty or ambiguity.
When applied to security training philosophy, an individual’s need for cognitive closure means that awareness training that doesn’t include an action they can do to “feel” more secure is more likely to generate panic or—worse—apathy over time.
How adtech uses cognitive closure in “activation” campaigns
It’s the same sort of cognitive closure levers that ad tech and marketing teams use to drive “activation” campaigns—that is, creating an experience to encourage participation for increased audience retention.
For example, can you remember the most memorable booth at the last security conference you went to?
Now, did it just look nice, or did you interact with the people or booth materials in some way?
Chances are, you’re more likely to remember the latter than the former.
By asking someone to engage during a booth visit—instead of just admiring the pretty design work and taking a pamphlet or two—the booth team is “activating” the individual through a cognitive closure loop:
- They posed a question or hypothetical scenario through the booth design, framing, and writing.
- They invited the visitor to answer that question or “prove” the proposed scenario through conversation, an activity, or some other interactive element.
(Speaking of which, if you’re reading this in March 2026—we’ll be at RSAC 2026 from March 24–27! Come exchange your old awareness training for something delightful at Booth S-263!)
Case study in action: A 10 minute video essay on net neutrality shuts down the FCC’s website
For another example on cognitive closure in action, let’s look at the viral “net neutrality” moment from 2017.
A new late night talk show host presented an extended video essay discussing “net neutrality”—an internet policy that many viewers didn’t even understand, let alone care about.
And then, once he’d educated his audience through humor and context? He gave them an action they could take to impact the outcome.
If I may revert to adtech terminology for a moment: the “net neutrality” segment’s call to action was so effective, that this brand-new show’s viewers accidentally crashed the Federal Communication Commission’s (FCC’s) website—flooding it with over four million comments on this previously unknown rule change.
If nothing else, this segment proves that even long training on boring topics can drive impactful change—which means your security training can, too!
Possible security actions beyond “stay vigilant” to drive your security training
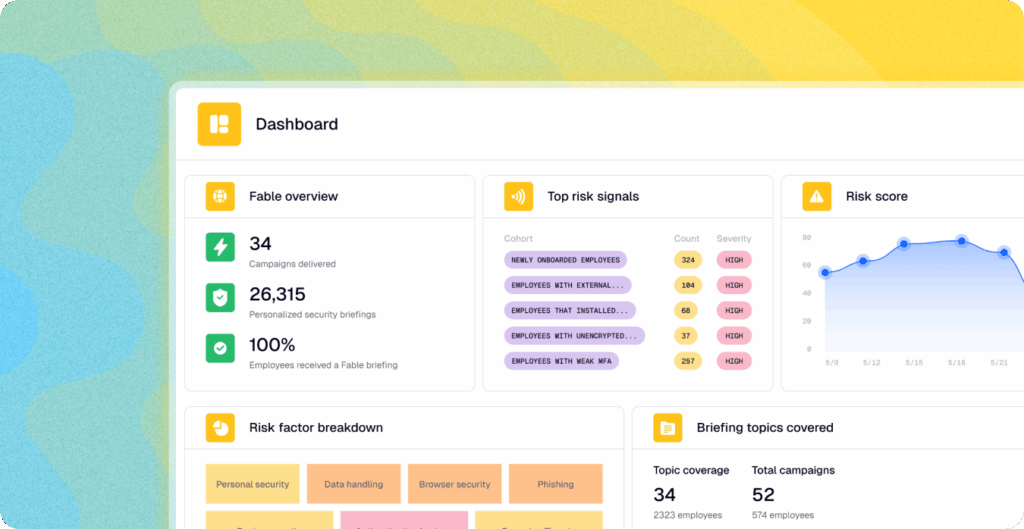
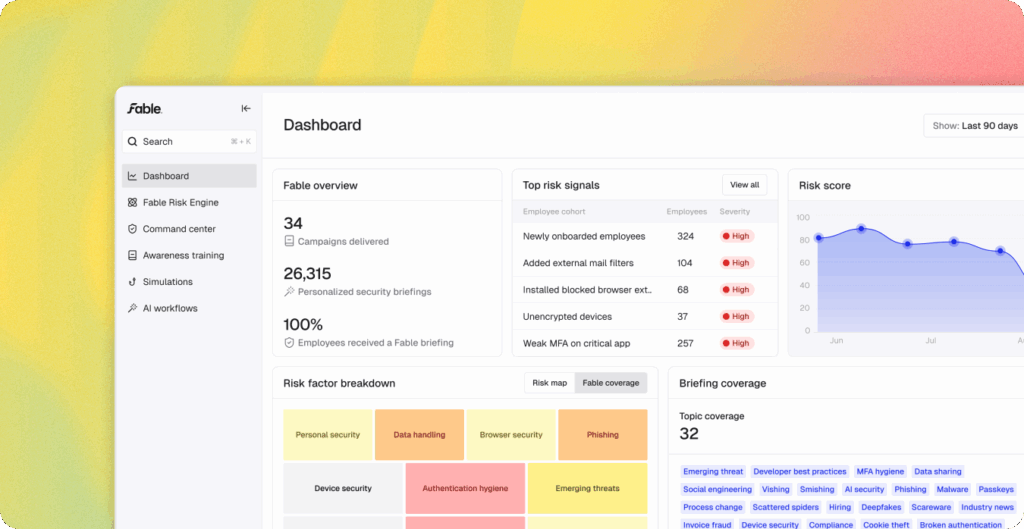
So when a Fable Security client asks us to create a new briefing, we’ll ask them what they’re hoping changes because they sent out this briefing—and help them think of ways to measure whether that change occurred.
For example, your security briefing could teach and encourage your employees to:
- Use provided password managers with pre-established password policies
- Seek out the approved software catalog list before searching for alternatives online
- Contact the correct cybersecurity team instead of “reply all” to every technology stakeholder
- Reach out faster when a possible breach occurs instead of assuming that “it’s fine”
- Adopt more secure tools, workflows, and policies with less pushback and friction
Of course, to measure true behavior change, you’ll need to establish a baseline of what your current behaviors are at your organization. Then, you can send out the briefing, wait for a bit, and then compare current outcomes to the known baseline.
That measured change over time represents the realized reduced risk as a result of your training: the changed behavior that decreased your overall human attack surface.
Repeat and iterate until your organizational behavior reaches your organization’s accepted residual risk threshold—and then maintain for all employees and onboarded new ones in a state of constant vigilance (to avoid the proverbial punch when their back is turned).
Next week, we’ll be discussing the impact of headline-driven briefings versus more cyber hygiene related training.
Meanwhile, you can read more about how behavior change impacts organizational resilience at scale on page 15 of “Modern Human Risk Management for Dummies”.