TL;DR—
Part three of six-part blog series on must-ask questions when creating net-new awareness training.
- After you figure out why you need new security training, next ask, “Who needs this?”
- The more targeted you can make your briefing, the more effective (and less annoying) your briefing will be.
- If you’re not sure who needs to get your training, consider who:
- Uses what software or hardware?
- Has advanced permissions or known security habit problems?
- Who is actively targeted by the specific attack?
- Can the recipient actually do something to make your organization safer?
- See “Five must-ask questions for security training that changes employee behavior” for more questions Fable Security asks our clients before creating short-yet-impactful briefings!
Thinking “everyone” needs your security briefing usually means no one pays attention.
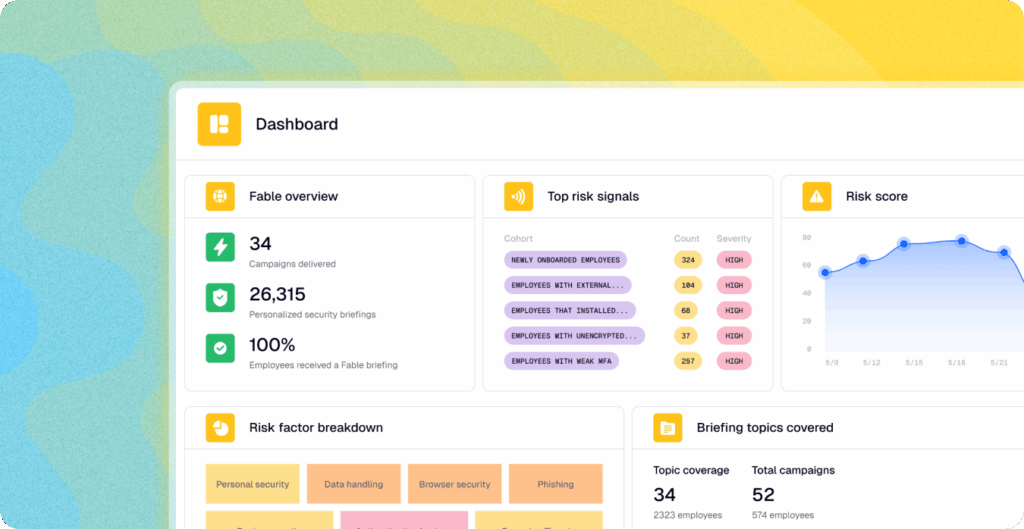
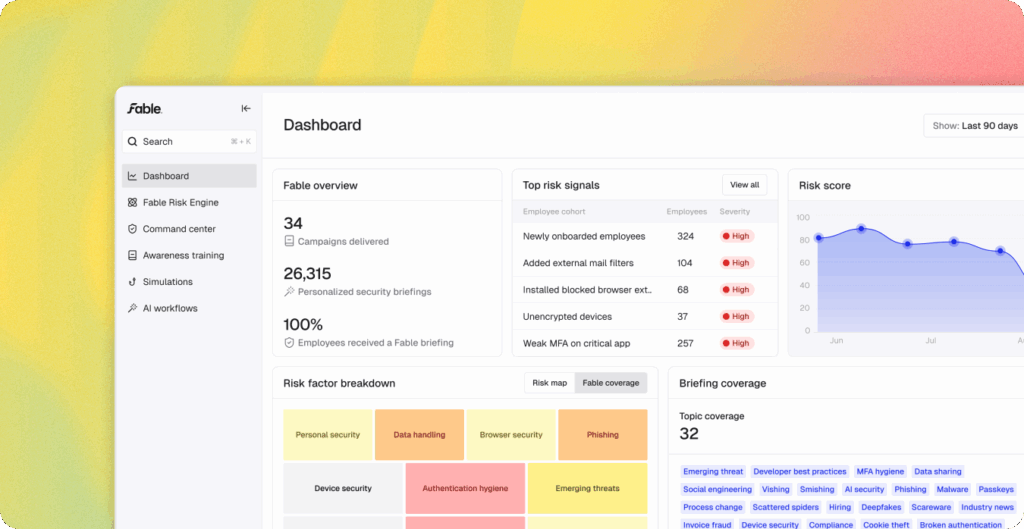
When a Fable Security client asks us to create a new briefing, we ask them for what cohort (employee group) they imagine would receive this new briefing—because who you’re talking to, dictates what and how you say.
Many new clients say that “everyone” at their organization should receive a new briefing, especially if it’s based on an attack that’s racing across headlines.
However, rarely does “everyone” in a company take the exact same actions to counter a trending threat.
Trying to put every action that any possible employee could take weighs down your briefing—forcing people to sift through a briefing or training to see what matters to them, personally.
In a worst case scenario, they might start to ignore or dismiss future security communications as irrelevant… even if something is extremely pertinent to their position.
Cohort case study: Scattered Spider’s 2025 attacks against U.S. insurance companies
Scattered Spider’s attacks on the US insurance sector in 2025 didn’t require broad awareness at companies in unrelated industries.
In fact, sending out an official notice or training to everyone could have prompted panic!
Even in an insurance or financial services-related organization, however, not everyone necessarily needed to be alerted to the attack or trained on the remediations.
Updated intelligence on this specific campaign showed that this threat group specifically targeted human resources and IT help desk staff with voice phishing (“vishing”) social engineering attempts to change passwords and employee information.
Therefore, a targeted alert and training on vishing remediations—with a special emphasis on sticking to established authentication procedures—sent only to the most at-risk employee cohort would avoid communications fatigue while increasing the briefing’s efficacy.
Example cohort groups for your new security training
If you’re still not sure who needs to receive your briefing, consider the following:
- Who uses, accesses, or manages the impacted software or hardware?
- Is the suggested security fix a backend control or detection that blocks attacks before they arrive?
- If so, only security and perhaps leadership need this information—not the whole organization!
- Who sees or interacts with attackers through phishing lures or social engineering attempts for this attack?
- Which individuals struggle with a good security habit that would allow or block an attack?
- Do you know who your money-handlers are?
- How much information is publicly available on your organization’s tech stack, major events, or management—all of which attackers research to craft a convincing lure?
- Who can plug jump drives and removable memory devices into their corporate computers?
- Which groups still have local admin access on their workstations by default?
- Who hates setting access permissions on files?
Really, the question of “who” can be answered by reverse-engineering desired outcomes: What could the recipient of your new training personally do (or not do!) that will make your organization more secure?
But, we’ll get more into that next week! You can sign up to get each blog as it comes out.
(In the meantime, we wrote more on how proper targeting impacts security training outcomes in “Modern Human Risk Management for Dummies” on page 9.)