The TL;DR
- There are compromised npm packages spreading malware
- It steals credentials and compromises your development pipelines
- Your developers are your primary defense; brief them quickly
- Scroll down for a free, 2-minute Fable video briefing you can use
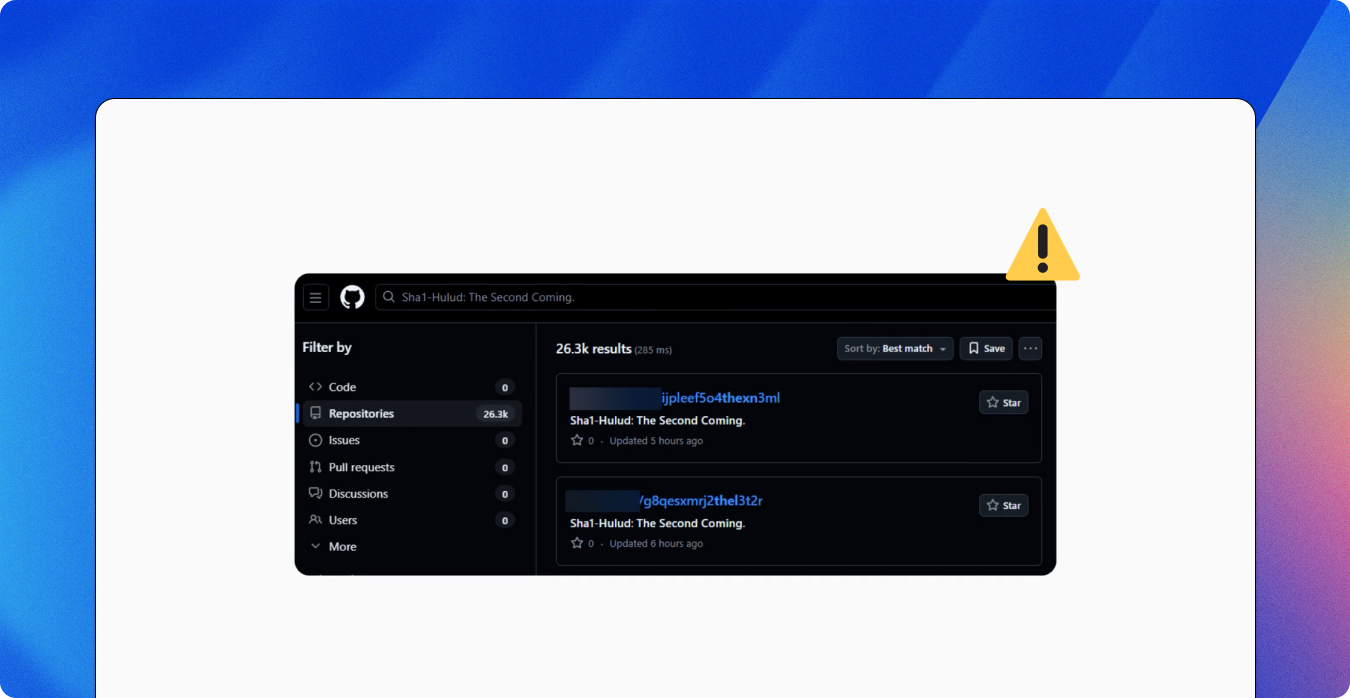
The Shai-Hulud malware campaign has quickly become one of the most disruptive npm supply chain events to date. Attackers compromised maintainer accounts and published malicious versions of legitimate npm packages seeded with credential-stealing malware. This means one compromised update can infect lots of organizations.
The worm malware steals sensitive credentials, including GitHub, npm, cloud, and CI credentials, by harvesting tokens from environment variables, local config files, and secrets exposed during CI builds. If it doesn’t find valuable credentials, it may try to delete local files. The attack can also derail development pipelines by injecting malicious GitHub Actions workflows designed to persist and steal more secrets.
Your developers are your first, and most affected, line of defense. Reduce exposure by briefing them about Shai-Hulud (and supply chain attacks generally), and urging them to validate updates before installing third-party software, use known-safe versions, and rotate potentially exposed credentials. Also, train them to disable automated install scripts where possible, and encourage them to flag unexpected prompts or behavior immediately.
To make it easy to brief your development teams, we produced a super-crisp, role-appropriate, personalized training video that explains Shai-Hulud in plain language and outlines the steps to take to safely navigate the threat. It’s available now inside your Fable platform and as a free download. It’s a fast, actionable way to alert your team about this and other supply chain threats.
Watch the briefing
And download for your own use below.
If you’d like risk-based briefings and nudges that are hyper-targeted and customized to your organization, try the Fable platform.